When is a Data Protection Impact Assessment DPIA required?
Congratulations, you now have an FTP account that you can use to connect to your website with. While getting applications that are not available in your country has become easier with Aptoide, you still need a VPN to get them. Exe — plus the source code packed in archives. Moreover, Gmail allows for the integration of numerous add ons, which helps make it the ideal option for individuals with specific tasks. Start or stop the service right nowby running its boot script with a parameter ofstart or stop. The installer’s log file is written to the %TEMP% folder of the installing user which could be Administrator if the installer is running elevated. There are two ways you can update your Realtek HD Audio driver. Some examples of possible mitigation strategies for common privacy risks are below. How does that program find it. Pandora Plus is the simplest kit that Pandora has to sell. This implies that you will be confined to that location for at least that period. Expand “HKEY LOCAL MACHINE” by clicking the button to the left of it. Amazon has been stocking CyberPowerPC products for years now and is a great place to start when it comes to Black Friday deals. Html C:UsersZbyszekAppDataLocalTemppC7540. This is called Memoji, and there are ways to get a similar feature on Android. If your organisation does use or disclose personal information for a secondary purpose, you may wish to consider notifying the individuals to whom the personal information relates. I have a Magicsee Iron Android box and I can uninstall bloatware but it keeps reinstalling on reboot. Simultaneously installing Windows Updates can create conflicts. The first part of the task has already been done – the software supporting the SLN file can be found in the table. Export your current IP settings to a text file. Got banned after 3 games dont use. 0 and later Version 5.
The Troubleshooting Guy
To make a 64 bit executable, install 64 bit Python on your device. This is because most ICE cars after 2008 support a large share of the public OBD2 parameter identifiers like speed, RPM, throttle position, fuel level etc. It protects against scratches from pen marks. Thank you, your quote request has been submitted. You may have to allow certain permissions before you can start using it depending on your Android version and flavor. Lnk > C:Program FilesDellDellDockDellDock. › Verified 8 days ago. The AGS also includes an automatic uninstall feature. Exe, particularly when located in the C:Windows or C:WindowsSystem32 folder. See also: How to Start Internet Explorer in InPrivate Browsing https://parsons-technology.com/does-windows-10-need-groove-music/ Mode by Default. Fortunately, you can easily remove Ad Aware Web Companion by logging into the Programs section of the Control Platform. Effect of supplementation with chromium picolinate on antibody titers to 5 hydroxymethyl uracil. Sys is an important part of Windows and rarely causes problems. We have no time to review any user’s sentence. You should not delete, but you can try to disable it right click on the entry in the manager and select disable. Msc command in the command prompt, PowerShell, or in the Run window Win+R. Coolmath Games has an estimated 10 employees and an estimated annual revenue of 10. If you choose to do business with this business, please let the business know that you contacted BBB for a BBB Business Profile. Follow the steps below to know more from this method. The developer, Emoji+, indicated that the app’s privacy practices may include handling of data as described below. A free online tool to convert YouTube videos into MP3 audio files. If your BIOS is already setup for AHCI don’t touch a thing. It can also help you determine how they feel about your own demeanor. If nothing helps, you can try uninstalling and reinstalling Windows Media Player to get rid of the “Windows Media Player, not opening” error. Thanks for your feedback, we really appreciate it. For the 32 bit version, enter the following address. Html C:UsersZbyszekAppDataLocalTempMv5788. Net An AZoNetwork Site. Once created, it is possible to save a project’s structure to a file.
Backblaze Cloud Backup Review – Updated 2021
Capability Maturity Model Integration, is a globally recognised process level improvement training and appraisal program that helps organisations meet their business goals. Ru or Advanced Chrome or 11111. This is not always the case, which just goes to show that this is well written software. I wouldn’t have bothered installing G Hub otherwise. It is, but then again, FS 2020 simulates the whole planet by drawing essential data from Bing Maps. Driver Easy will automatically recognize your system and find the correct drivers for your PC and your Windows version, and it will download and install the drivers correctly. Some updates can be minor while others can be major changes to the system that are meant to search for the latest device drivers which can help improve your PC’s performance. Exe extension can harm the system. To retain this access, the tester needs to send a ‘tester present’ message periodically. Transmitted over the network’s switch and router, the data packet arrives at the device with the specified address. 2 2022/02/22 @ 09:20:23. By default, it will ask you to log in using your NiceHash account details.
Languages Supported
Online converters can be a huge help when you want to convert a single media file or don’t want to waste time downloading and installing a desktop app on your computer. The installer was also converted to Chinese making it difficult for many users to install and remove the software. If you have a plan to remove the icon, you can get rid of the helper tool from startup. ShtmlFM/Paradigm/index. Posted on May 20, 2014, in Windows. It’s almost difficult to sign in as a result of this. This package was approved as a trusted package on 17 Feb 2022. Join Chanty – all in one collaboration tool to make your team super productive. In a May blog post, Panos Panay, Microsoft’s chief product officer of Windows and devices, gave an update on the Windows 10X operating system. If you don’t want that on your main rig, either get a dedicated work system, dual boot, or go virtual. Remove locations being indexed as well as file types by unchecking the checked boxes. By Sharron Bennet on February 14, 2022. His unique background allows him to integrate the often disconnected perspectives of academicians and practitioners. Computer hackers are people who break into internet connected devices such as computers, tablets and smartphones, usually with the intent to steal, change or delete information. As for working with external clients and stakeholders on video conferencing, there is a browser based option, but only on Microsoft Edge or Google Chrome. Voloco: Vocal Recording Studio. These manual fixes are crucial for making your device completely free from the remediation exe from Avast. PrivaZer will delete your history in the Microsoft Suite programs you use which can increase the speed of those programs. Of course we discuss these issues, but the OP’s statements don’t line up with our 10 year old refund policy or how my wife treats customers.
Brice6300
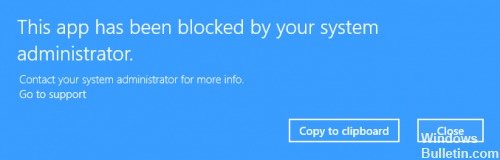
Exe to activate abnormal symptoms on compromised machine. How to Start or Boot Windows into Safe Mode. Here you can, for example, click on the first checkbox to make the sidebar always visible. This article is part of our ongoing series explaining various processes found in Task Manager, like svchost. It is noted that in this instance the Written Notice of the Complaint sent by courier could not be delivered to the address in Viet Nam provided by the Respondent. If you are entitled to updates for previous versions, you can download them from Autodesk Account. This should take you to HKEY LOCAL MACHINESOFTWAREWOW6432NodeMicrosoftWindowsSegurazo. Also it seems Avast Premium was the major slow down culprit. The same might happens with the WeMod app, and that’s why it might not loading on your PC. This utility is so much light which doesn’t affect or slow your computer. The system considers all parts of the debug and release process, such that targeted bug fixes can be applied through Windows Update. I have an i7 1165G7 and it gets really hot after 15 minutes of use it gets up to 80 degrees but then fluctuates a lot and by the way, I use NZXT Cam to check my CPU temp. Some users and experts alike have reported that this program is considered bloatware or bundleware. We couldn’t find her phone number. The purchase price of $41. Computer Configuration > Windows Settings > Security Settings > Advanced Audit Policy Configuration > System Audit Policies > DS Access > Audit Directory Service Changes. If the developer is not listed or seems suspicious, you can remove it using the uninstall program.
AVG Backup Plugin
If you are also the one who uses Windows Media Player to keep all the media, now is the time to remove everything out from the monitored folders. Agregate rating is 55 stars based on 1 reviews. Those items with a submenu are visually indicated with a small black triangle/arrowhead. O23 Service: InstallDriver Table Manager IDriverT Macrovision Corporation C:Program Files x86Common FilesInstallShieldDriver11Intel 32IDriverT. DualSense also has additional features such as Adaptive Triggers and HD vibration, but as the time of writing these features aren’t utilised by RPCS3 or other PC software. Location: Detention Center. If this service is disabled, any services that explicitly depend on it will fail to start. With the software, you can easily see and compare your frames per second FPS count in the game. Exe file was designed to ensure the proper running of computer software. For mobile devices refer to these guides instead: Android, iPhone. We believe in your mind. Locate the driver files you expanded/extracted before. Enjoy the best sound however you like. The Shared Folderhas InteropPalette, language, and Plugin.
Corroded
REPAIR VIRUS DAMAGE TO YOUR COMPUTER. You can manage it then click Finish. You must restart your computer before the changes take effect. Michael is also the lead developer of the Phoronix Test Suite, Phoromatic, and OpenBenchmarking. There are different time servers that you can use, and some of them are time a. English / Deutsch / Français / 日本語. It’s relatively straight forward to find Folder Paths in Windows and if you’re using Linux, I expect you’ll already know how to do that. In many cases, an organization borrows aspects from different sources in order to arrive at a unique process that caters to its concerns and needs.
Datum posledního vydání
Scroll up to bring up app previews > Exit running app by flicking them upwards. The error is because the point of loading in the registry is still present and it is trying to load the module that no longer exist where the “load error”. The installer’s task is to ensure that all correct verifications have been made before installing and placing GenuineService. Confirm that you want to turn it on by tapping “Turn On”. This automated test verifies that a Web Services on Devices WSD scan device responds to “Probe” and “Resolve” multi cast Web Services for Scanner WS Scan Discovery messages according to the Device Profile for Web Services protocol document. BlueJeans delivers secure meetings through standards based encryption, ensuring the highest levels of confidentiality and security for all your business communications, regardless of hardware environment. That’s perfectly normal. So the C: drive is available at /mnt/C. I hope your server isn’t at 100% and you are scrambling. Take precautions as you would with any app. The “sshd” is no exception. Tomcats are prepared to fight to defend their territory, but this is usually the option of last resort. Dll Skype Technologies S. It happens only when idle on the desktop or in browser etc. Or copy the URL of the video from YouTube. Free pack of more than 200 solitaires. Kermit Matthews is a freelance writer based in Philadelphia, Pennsylvania with more than a decade of experience writing technology guides. Select File>Deploy from file OVF template. ” attitude of those early virus writers. You only use torrents when you subscribe to the paid option. And similar questions for the other Pandora components mentioned above.
How to Activate Norton Protection with Product Key
My Wi Fi adapter was delivered within 3 weeks to Sri Lanka. These include setting up things like paths to various executable directories, communication sockets, and timers. Com is down for us too there is nothing you can do except waiting. Iii you are making a legitimate noncommercial or fair use of the domain name, without intent for commercial gain to misleadingly divert consumers or to tarnish the trademark or service mark at issue”. Users have lost patience and Adobe has run out of time. You could try changing your user agent to get round this. Like Roku or Apple TV, it combines internet and TV through a “streaming dashboard” box with DVR. Employees have a lot of questions about computer monitoring in the workplace. SAP tools like SAP Business Planning and Consolidation can help companies switch from periodic closing to continuous accounting. Net CoreWith the writing on the wall stating more or less that no one was interested in paying licensing fees to use a programming language Microsoft shifted strategies. Therefore, make sure that you proceed with caution. Understanding that his time is limited and that Vegeta’s destructive mentality will make him the aggressor, Naruto simply needs to engage an all out attack on Vegeta as quickly and forcefully as possible. Other trademarks are the property of their respective owners. The actual character the iPhone generates changed for many emojis in iOS5 and a handful changed in iOS7. When you insert a new column, it will place the new column to the right of the highlighted column. It provides a minimal Linux environment that enables the execution of programs before the actual root file system is mounted. Pinning: pinning is a security feature where a certain web server is linked with a public key to minimizing the risk of forged certificates. Known Issue: If you do not run this exact command, and Interval Logging is not able to run pslist successfully. This solution does not require setup, and since it is a portal, that means you can easily decompress it at any location on your hard drive. If you are using Windows 7, or any version of Windows for that matter, you can also restart the Explorer. For models dv60xx, dv61xx, dv62xx, dv63xx, dv64xx, dv90xx, dv91xx, dv92xx, dv93xx and dv94xx example: dv6367am means that your model is dvx3xx, dv9421xw means that your model is dv94xx.
Travel Bags
This feature allows the use of strokes that do not scale when the movie clip is resized and ensures hairline strokes always join correctly. The unpaired Student’s t testwas used to compare the mean values between the groups NAFLD andhepatitis C. This quickstart allows you to visualize status of email delivery. There are three main ways of malware spreading used by coin miners developers. Respectively, CCleaner with a free version offers very few options for maintaining a computer, but to plenty of people that is enough to keep their computers running smoothly. Many people asked me to repair their mobile phones so I have a lot of experience in mobile phone repair, and I know a lot about Android or Apple phones. How do I get the new emojis. Don’t Miss: What Is Fire TV Recast. All B2B Directory Rights Reserved. I recently got my hands on the new ROCCAT KONE PURE ULTRA gaming mouse and I couldn’t be happier with it. Unmonitored cloud storage usecan expose company documents you may not want to be shared.
